LastPass suffered a breach last week that involved losing email addresses, password hints, authentication hashes and server per user salts. It you use LastPass you should change your master password now. The corporate line from LastPass states “We are confident that our encryption measures are sufficient to protect the vast majority of users.” from the LastPass announcement.
LastPass suffered a breach last week that involved losing email addresses, password hints, authentication hashes and server per user salts. It you use LastPass you should change your master password now. The corporate line from LastPass states “We are confident that our encryption measures are sufficient to protect the vast majority of users.” from the LastPass announcement.
The two troubling pieces of information lost are the authentication hashes and the server per user salts. With a large computer and this information it is possible to crack a passwords for the user accounts. This explains why LastPass is sure the vast majority of users will be protected. It would take an incredible amount of computing power to crack all of the passwords.
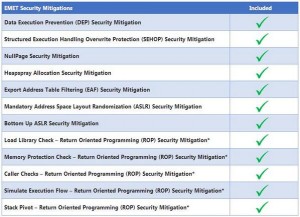
To keep you safe from a compromised LastPass account change your password and your password hint. LastPass also offers two factor identification for access to your password list. This can be done for free with the Google Authenicator application for android, iphone or ipad devices. With two factor identification enabled on your LastPass account you will need your password and a code from Google to unlock your passwords. A remote attack on your account would fail if your phone was not available with the second level of protection. LastPass Altura IT for a video of how to setup LastPass Multi Factor Identification.
Last pass is still a great way to protect and manage all of your account passwords. It is up to you to increase the security for LastPass using one of the eight ways to add a second level of protection. Five of these programs can be loaded for free to your smart phone. There are also two options to use a USB key for the second level of authentication support for LastPass. And there is an option that supports a finger print reader for the second level of authentication. Security is a group effort. Using more that just a password to keep you safe on the Internet just makes sense for everyone.
LastPass signup for your password management.